What are Frame Grabbers?
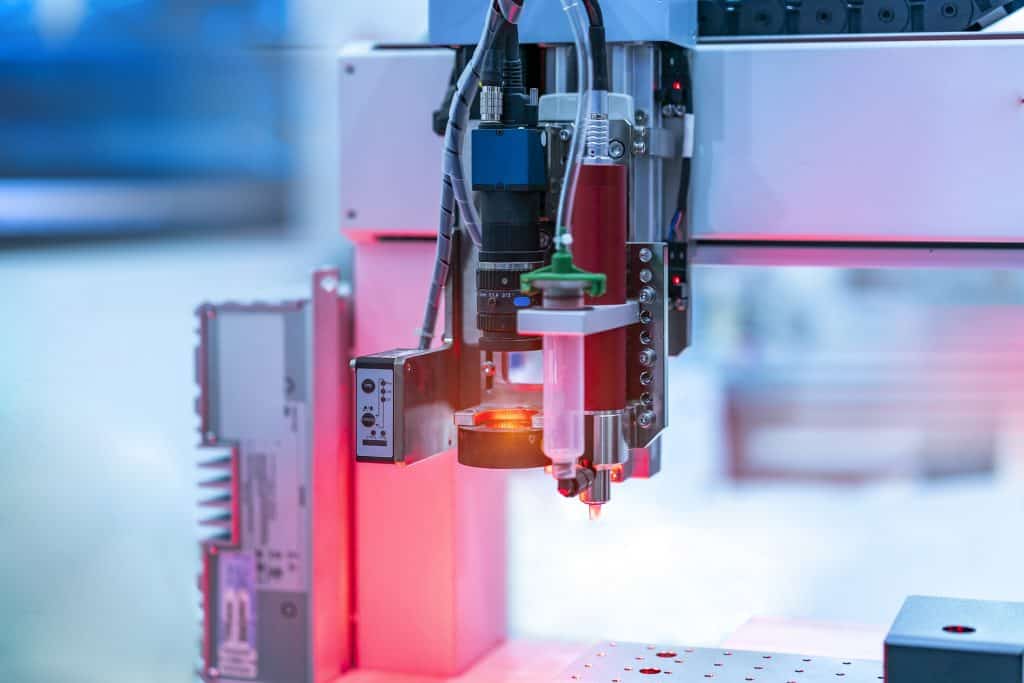
Have you ever paused a movie to get a closer look at what was happening? Frame grabbers work a little something like that, in that they can capture still photographs from videos. However, frame grabbers are far more advanced than a simple pause button. In fact, frame grabbers are often used to acquire precise images in medical applications, scientific research, security surveillance footage, industrial automation, and machine vision.
The technology behind frame grabbers not only captures higher quality images but also transfers important data from each captured image to a computer for analysis. Discover more about Frame Grabbers for machine vision system and how they can improve and streamline your processes.